A researcher has hacked into IT systems of some of the largest corporations in the world. Alex Birsan, a Romanian researcher has successfully assaulted Apple, Microsoft, Tesla, PayPal, Netflix and over 30 other corporations.
Birsan said that he advised the companies in advance that he would test the security of their systems, but did not provide them with details beforehand.
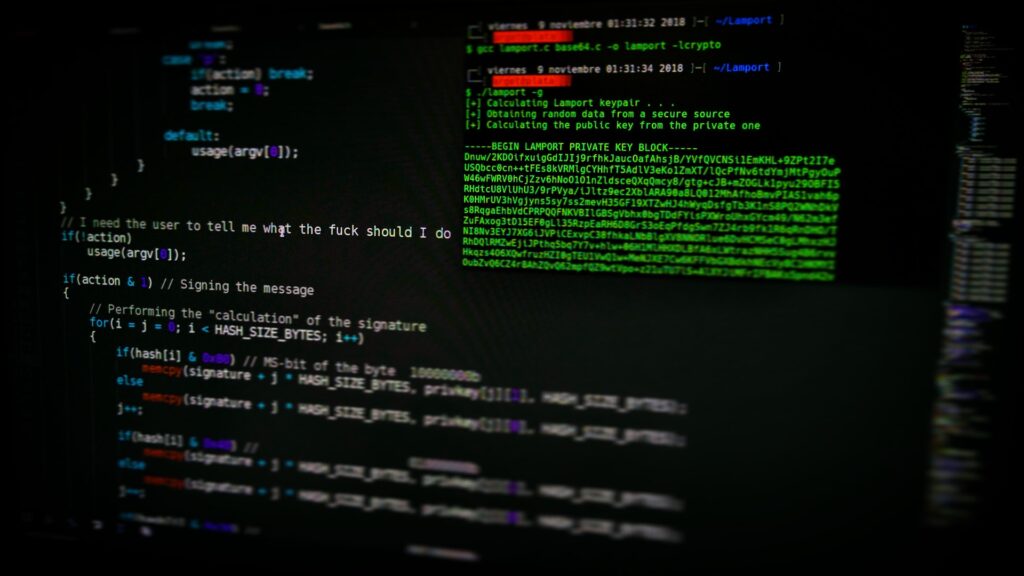
He did the attack simply by replacing private code packages routinely activated by servers with public code packages.
The automated systems used by companies tap into public repositories when it requires a code package. When needed, the system will automatically swap a public module for its own in-house one if it detects an identically named package it believes is a newer version.
This brought into light the vulnerabilities or design flaws in automated build or installation tools which could cause public dependencies to be mistaken for internal dependencies with the same name.
He took advantage of this loophole and injected code into packages stored in public repositories such as GitHub. Birsan termed this as dependency confusion, which is an intentional duplication of names and subsequent swapping of files.
However, he had to find the names companies used for the code files so he could create counterfeit files with the same names, but he found that task to be relatively easy. An example was Shopify had a name Shopify-cloud which Birsan guessed correctly.
Birsan added that the success rate was astonishing and also they were able to automatically scan millions of domains belonging to the targeted companies and extract hundreds of additional JavaScript package names which had not yet been claimed on the npm registry.
A malicious code could wreak havoc throughout a company’s network, disrupt operations, steal data or attempt to extort money. Birsan’s code was not malicious as he retrieved only basic information about each computer his code impacted including username, hostname and the current path of each unique installation.
“Along with the external IPs, this was just enough data to help security teams identify possibly vulnerable systems based on my reports,” Birsan said, “while avoiding having my testing be mistaken for an actual attack.
Birsan collected ‘bug bounty’ cash that companies payout to researchers who uncover vulnerabilities. He got a total of around $130,000.
The idea popped up when Justin Gardner, Birsan’s colleague, examined an internal JavaScript package managing file and wondered what would happen if an identically named file were placed in a public repository.
They found whichever file had the most recent build number would be tapped by the company’s server.
“Specifically, I believe that finding new and clever ways to leak internal package names will expose even more vulnerable systems, and looking into alternate programming languages and repositories to target will reveal some additional attack surface for dependency confusion bugs,” he said.